Law, Order & the Making of Money
Laws and regulations often keep, generate, or even increase business, revenue and profit for security companies.
Tired of all those silly laws? Weary of the tax-sapping and job-killing regulations? Critical of bureaucrats that make decisions but don’t know or care about your business? Listening too much to the cable and radio talking heads spinning out doom and gloom?
Hold on. Simmer down. Switch off the TV. It turns out that most laws and regulations, including those being considered today, are not directly aimed at the security industry and its dealers, integrators, installers, and technicians but at their customers and clients. The somewhat secret indulgence is that these laws and regulations often keep, generate, or even increase business, revenue and profit for security, life safety and building automation.
Still mad?
Maybe all those scalding-hot-cup-of-coffee lawsuits make your blood boil.
Well, how many security video cameras would be in parking garages or on the wall of an office lobby without the peril of a six- or seven-figure liability fight?
And, if you think that the Department of Homeland Security (DHS) is just a lumbering boondoogle, well, many in the security industry see it differently. While DHS’s overall mission is huge and daunting, its impact through programs, projects, directives, infrastructure focus, research, and collaborative work with the private sector has been a major influence on technology, products, and commercial and corporate buying — beyond just government and its contractors.
Some Can Harm the Business
No doubt, some laws and regulations can potentially harm, especially when it comes to licensing and taxing of security businesses on a state-by-state or federal basis; over-zealous application of false alarm solutions by municipalities; and energy efficiency of equipment, to name three areas.
Looking for quick answers on security topics? Try Ask SDM, our new smart AI search tool. Ask SDM →
When it comes to licensing, organizations such as the Custom Electronics Design & Installation Association (CEDIA) and the Electronic Security Association (ESA) carefully track licensing activities in legislatures to educate elected officials and their staffs to ensure that measures reflect what dealers really do and need to know, according to CEDIA’s Director of Public Policy Darren Reaman. ESA’s State Licensing Guide is ever updating. “We have strong chapters” who help keep an eye on things weekly that then leads to a monthly report, says John Chwat, ESA’s director of government relations.
Wording in one proposed state bill, Reaman points out, may have mandated a two-year apprenticeship if an installed touchpad would integrate with HVAC, among other subsystems. Thanks to CEDIA involvement, that did not happen.
When it came to taxing of small business, ESA, among others, was part of a drive to repeal the 1099 reporting requirement passed within healthcare legislation last year. ESA pointed out the requirement would place a heavy burden on the backs of the small business owners. In April, Congress passed the repeal and President Obama signed it into law.
Another issue that Chwat and ESA track is state legislation which places restrictions on automatic contract renewal. One example: In Texas, a bill is being considered and ESA is working with the local industry association to defeat this measure’s impact on the industry.
Also of concern: Municipal and state “pressure on their budgets makes our industry a target,” adds Chwat. In Virginia, for instance, the firefighters union proposed a tax on central station — $2 per client per month — which died. But the idea “is now going from the state to the counties,” he adds.
More all-encompassing, there has been some movement, like a proposal in Illinois, to allow fire protection districts to engage in the fire alarm monitoring business. It allows fire districts to mandate that everyone use the fire district’s monitoring business. This, too, could spread to “cities and counties offering our types of services,” Chwat says.
Then there are concerns over fire sprinkler ordinances and proposed laws. ESA is requesting Congress to include amendments to the Fire Sprinkler Incentive Act of 2011 that would provide a “balanced approach of fire suppression + detection = fire protection,” according to an association statement. The bill proposes tax incentives for the purchase and installation of sprinkler systems. But it, and some other state and local measures, are “leaving the impression that suppression systems are the only way to go,” Chwat points out, and who wants such legislation to be broader to include ESA services, too.
A potentially pro-industry proposal to some, the Electronic Life Safety and Security Systems Federal Background Check Act of 2011 establishes a system of FBI background checks for employers and employees. Some states don’t “license our part of the industry” and that situation encourages “unsavory individuals” to get into the business, adds Chwat.
When it comes to impact on ESA members, cloud computing may be the next big thing. “Here we get involved but also brief members” on emerging business opportunities in addition to threats to the business, comments Chwat. On the regulatory side, the Federal Communications Commission is moving into the broadband era. “We help dealers plan strategically.”
More all-encompassing, the Security Industry Association (SIA) has an eye on potential laws and regulations that might over-burden product and system manufacturers, which would raise the price of goods to dealer and integrator resellers.
There are also off-and-on legislative efforts that could slow down the security parade.
What seems to make lawmakers and regulators salivate can be summed up in two areas: privacy and biometrics.
The Privacy Issue
What started out as a “leave me alone” concept, privacy has vastly expanded, especially because of the growing concern of business breaches and so-called identity theft.
SIA took a strong lead on privacy protection issues with the release of a Privacy Framework. It addresses privacy concerns related to the recording of video, the collection of personally identifiable information and the use of biometrics, radio frequency identification (RFID), and other security technologies. It identifies a number of guidelines to be followed in the deployment of electronic physical security solutions, including:
• conducting privacy impact assessments;
• implementing privacy-enhancing solutions during the design phase, when possible;
• limiting access to personally identifiable information within an organization to those who have a “need to know”;
• adopting a security breach notification plan; and
• establishing a retention policy for personally identifiable information and a procedure to ensure that such information is destroyed at the time stipulated by the policy.
“Compliance issues and regulations can create market opportunities,” says Donald Erickson, SIA’s director of government relations. Dealers and integrators with an understanding of their clients and regulations and laws their clients face can provide solutions that go beyond security and life safety.
One example: The Health Insurance Portability and Accountability Act (HIPAA) mandates that certain businesses in the healthcare industry better protect data and patient information. A higher level of access control and surveillance of records is one outcome. At times, security video also must be positioned to meet HIPPA requirements. The Health Information Technology for Economic and Clinical Health (HITECH) Act, which came later, expands requirements into associate businesses, often including corporations that maintain health records of their employees.
RFID Worries by State
Proposals in California, New Hampshire, and Maine have aimed at radio frequency identification and an alleged ability of some to “grab” personal information during a transaction or — more Buck Rogers like — being near a person with an RFID card. SIA and its members, including HID Global, have educational efforts in place to play a role in such dialogs.
While lawmakers and their constituents today are less likely to be concerned about security video, even in public areas, there are some that feel less comfortable when it comes to biometrics. But times are changing.
Enterprises, slowly but surely, are moving to smart cards with a biometric, in addition to niche applications at data centers. There are ePassports and an alphabet soup of government and military identity cards.
Another biometrics battleground may be the federal voluntary E-Verify program. U.S. law requires companies to employ only individuals who may legally work in the United States — either U.S. citizens or foreign citizens who have the necessary authorization. E-Verify is an Internet-based system that allows businesses to determine the eligibility of their employees to work in the United States. Congress is considering changes to the program.
And SIA has a paper that provides recommendations for the use of biometric technology in the program. It followed another SIA effort that more generally endorsed the concept of adding biometrics, according to Tom O’Connor, SIA’s manager of government relations.
FIPS 201 Gets Revised
More expansively, major revisions of the Federal Information Processing Standard FIPS 201-2 specifies the architecture and technical requirements for a common identification standard for federal employees and contractors. The overall goal is to achieve appropriate security assurance for multiple applications by efficiently verifying the claimed identity of individuals seeking physical access to federally controlled government facilities and electronic access to government information systems.
According to CertiPath CEO Jeff Nigriny, there are major changes in the proposed revision of FIPS 201-2 of interest to integrators, whether they serve government clients or enterprises. “Iris biometrics will become a valid biometric in addition to finger. Biometrics will be embedded on the Personal Identity Verification or PIV cards.” In addition, physical access must match what is taken at the door to what is in the physical access control system (PACS). And the unique identifier within the badgeholder ID kind of shifts things around with the power to check everything on the card and not necessarily on the PACS.
For dealers and integrators, FIPS 201-2 will create business opportunities beyond the original FIPS 201 with PIV i (for interoperable) and c (for compatible) card readers, software, smart cards, and consulting.
Thanks to laws, regulations and government directives, there are also opportunities in specific types of industries as DHS moves along the risk chain.
Chemical Facility Anti-Terrorism Standards (CFATS), as developed by DHS, establishes risk-based performance standards for the security of chemical facilities. It requires facilities covered to prepare security vulnerability assessments, which identify facility security vulnerabilities, and to develop and implement site security plans, which include measures that satisfy the identified risk-based performance standards.
According to Erikson, CFATS covers many facilities and not just large chemical plants. “Facilities are tiered from one — the most at risk — to four. There have been about 39,000 assessments. And through DHS analysis, about 4,000 have been tiered, with about 110 ranked in tier one.” Erikson sees business value for security firms to know more about the program and how they can be involved. Information and involvement are accessible. “There is a help desk at (866) 323-2957 or at http://csat-help.dhs.gov. And some expect the program will enlarge to include safe drinking water and wastewater facilities.”
Transportation Worker Requirements
Another DHS mandate through its Transportation Security Administration, which holds growth for dealers, integrators, and product manufacturers, is the Transportation Worker Identification Credential or TWIC. It is a vital security measure to ensure individuals who pose a threat do not gain unescorted access to secure areas of the nation’s maritime transportation system. Established by Congress through the Maritime Transportation Security Act, TWICs are tamper-resistant biometric credentials issued to workers to secure areas of ports, vessels, outer continental shelf facilities, and all credentialed merchant mariners.
“There are about two million workers who have applied or should apply,” O’Conner says. “The TWIC card reader program is in pilot but, according to the General Accounting Office, there is a high degree of failures.” So welcome to integrators to help solve the problem.
For some dealers and integrators seeing business in work identity, credential and access management or ICAM, that may prove to be the sweet spot, contends Joe Gittens, SIA director of standards.
Identity Credentials
The mandate’s mission is to foster effective government-wide identity and access management, enabling trust in physical and online transactions through common identity and access management policies and approaches, aligning federal agencies around common identity and access management practices, reducing the identity and access management burden for individual agencies. Emphasis is on common interoperable approaches, ensuring alignment across all identity and access management activities that cross individual agency boundaries, and collaborating with external identity management activities through inter-federation to enhance interoperability.
Then in February, the Office of Management and Budget issued Memorandum M-11-11 directing agencies to require the use of the PIV credentials as the common means of authentication for access to facilities, networks, and information systems.
John Bartolac of Axis Communications sees that, especially on the federal level, laws, directives, and regulations can “cause confusion.” But it might pay off for the persistent dealer or integrator. “It’s obvious that Homeland Security is the biggest driver” for purchases, he adds. Bartolac sees opportunities in the near term when it comes to cybersecurity, sometimes blended with physical security. He suggests that a next big field to mine is included in the Federal Cloud Computing Strategy, a report issued in February by the White House’s Vivek Kundra, U.S. chief information officer.
There is coming a time, says Bartolac, when government agencies — local, state and federal — as well as government and military contractors and other enterprises will not be able to purchase products, systems, or services without complying with myriad existing and emerging directives, rules and regulations.
Of course, when it comes to laws and regulations, there are smaller fish to fry outside of the federal waters.
For CEDIA’s Director of Public Policy Darren Reaman, it is often a matter of keeping ahead of the technology as well as the legislators. “Systems and types of equipment change. They are technology-based and ever changing. There also is the dynamic of politics. Licensing should aim at five or 10 years down the road. But that is not always possible.” Public officers and regulators change jobs more often than the technology.
| Pasadena Refining: Software Helps Register TWICs in PACS | |
|
Pasadena Refining Systems, a subsidiary of Petrobras America., has deployed a FIPS 201 solution to register Transportation Worker Identification Credentials (TWIC) into its physical access control system (PACS). A mobile validation software application can verify PIV, TWIC, and other types of corporate and government credentials. With PIVCheck Plus from Codebench (www.codebench.com) the refinery is able to read, validate, authenticate and register TWIC cards into the facility’s physical access control system while verifying the authenticity of TWICs presented to a Datastrip mobile biometric reader. The software also can tell the operator whether that TWIC is already registered in the traditional access system and, if so, whether the cardholder is allowed into the facility at that time. “We’re being proactive with our TWIC usage at our facilities,” says Eric Finck, security supervisor at Texas’ Pasadena Refining Systems. It is all part of a major security upgrade, which was in part paid for through the Port Security Grant Program. The program is designed to provide funding for transportation infrastructure security activities to implement Area Maritime Transportation Security Plans and facility security plans. Consulting firm Transportation Security Associates provided the refiner with its grant-writing expertise, helping the petrochemical firm secure grants to pay for various security upgrades. In addition, the firm provided program management for the project, which involved security assessment, planning and design for integrating TWIC credentials into the refinery’s access control system. The facility uses two desktop biometric smartcard readers to register TWICs and six handheld readers to check TWIC cards of employees and visitors
PHOTO COURTESY OF CODEBENCH |
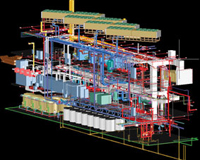
| BIM Bam: This Model Is Hot | ||
To better meet building codes, laws and regulations, integrators are finding value in building information modeling (BIM). It is the process of generating and managing building data during its lifecycle and involves representing a design as objects — vague and undefined, generic or product-specific, solid shapes or void-space oriented (like the shape of a room), that carry their geometry, relations and attributes. BIM design tools allow for extracting different views from a building model for drawing production and other uses. These different views are automatically consistent in the sense that the objects are all of a consistent size, location and specification because each object instance is defined only once, just as in reality. Security, life safety, computer, communications, and HVAC systems can be modeled into BIM. They can be easily changed in new construction and remodeling plans as requirements and regulations change. |
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!