The world is not the same as it was pre-COVID-19, businesses included.
“The complexion of the work environment has changed dramatically due to the pandemic,” says Jody Ross, vice president of sales, AMAG Technology, Hawthorne, Calif. “Many organizations have shifted from large office spaces to more hoteling-like scenarios.”
And, with the rise of hybrid work and a come-when-you-want office model, workers past and present are now digging their keycards and badges out of their wallets. However, loose credentials are a security risk. And, they carry more germs, which is risky when trying to make a safe return to office. Frictionless solutions also keep workers productive.
“The more frictionless experience customers have or occupants of a building have in accessing a building, the more productive they are, the more time they save,” says Sheeladitya Karmakar, global offering leader, enterprise security, Honeywell Building Technologies, Atlanta.
This frictionless experience is becoming more common in buildings looking to revamp their readers, with mobile credentials taking the lead.
“The right mobile credential can provide tremendous opportunities to enhance the user experience for integrators, their customers, and individual users alike,” says Scott Lindley, vice president and general manager, Farpointe Data, San Jose, Calif. “Integrators appreciate when the order process for mobile credentials is identical to what they’ve been used to for years with physical credentials.”
Trends in Readers & Credentials
Despite mobile credentials becoming more popular, the move away from keycards has had some slow adoption.
“The adoption of using a smartphone has been slow, since using traditional passive credentials systems are cheaper and simpler for tap-and go-access for the user, versus waiting for an app on the phone to authenticate,” says David Ito, project manager, Camden Door Controls, Ontario, Canada.
Although still used, 125kHz proximity cards are on the way out, according to the experts, since they’re easy to replicate.
“Providing credentials and keeping them updated could be challenging,” Ross says. “That is why companies have started to shift towards using mobile devices for credential management. Permissions and administration can be done remotely, keeping the credentials up to date at all times.”
The digital revolution has also increased the desire for mobile credentials and touchless, frictionless access.
“As everything we touch becomes digital, and we rely on our mobile devices for more and more of our everyday activities, seamless access is becoming more of an expectation than an aspiration,” says Jake Fergerstrom, product manager, readers and credentials portfolio, Allegion, Carmel, Ind.
Additionally, mobile credentials are on the rise simply because it’s difficult to lose something you have on your person at all times.
“Given the choice, most users would prefer the use of mobile technology over a physical device, so providing options and driving awareness is key,” says James Reno, vice president, commercial sales, Alarm.com, McLean, Va.
Mobile credentials come with many added benefits for users.
“First and most obviously, they are right on your phone, so you no longer need to juggle or remember a physical card or fob,” says Mike Green, product manager, BlueDiamond ecosystem, LenelS2, Pittsford, N.Y. “But beyond that, they are highly customizable and can enable things like hands-free entry based on user-programmable proximity, shake-to-open for entries with turnstiles and more. Mobile credentials are also much simpler to provision, de-provision and manage, making them a boon for users and security or building personnel alike.”
Mobile credentials are also revolutionizing safety in office buildings.
“The market was starting to slowly transition to Bluetooth readers and mobile technology before the pandemic, but now security teams are finding the budget and prioritizing the upgrade,” Ross says. “The pandemic has shown the need for touchless solutions once in the office, and for solutions that require remote setup for employees who continue to primarily work from home.”
Mobile credentials are also reducing the hardware footprint around the door, making access control more accessible for businesses.
“Mobile technologies are poised to disrupt and provide better paths for adoption and technology refresh,” Reno says.

Physical credentials, like keycards and keyfobs, still have a place in access control despite the rise of mobile credentials. // IMAGE COURTESY OF ALLEGION
The End of Keycards & Fobs?
With all the talk about the benefits of mobile credentials, keycards and fobs must be on the way out, right? It’s a mixed bag, according to those interviewed. Some believe that both near field communication (NFC) keycards and fobs will be used in tandem with mobile credentials.
“I don’t believe the widespread use of mobile credentials will signal the death of cards and fobs,” says Lindley of Farpointe. “While we can do a great job of educating users to alleviate any perceived fears of going mobile, there will always be some who don’t want access control functionality on their phones. It’s not an either/or scenario, as integrators today can offer seamless mobile solutions — for proximity or contactless smartcard installations — that give access control administrators the ability to have both mobile and physical credentials within the same system.”
Fergerstrom of Allegion adds, “There are several challenges that mobile credentials need to solve for before we expect to see mass adoption across the industry. Opportunities for improvement include consistency in the user experience, cross-platform functionality, and the need for a physical identification badge in many sectors, among others. We do, however, expect to see shifts in the mix of our plastic credential business over the long term in favor of our mobile Bluetooth and NFC credentials.”
Some believe that keycards will endure.
“Not only will physical cards endure, but there will be more choices for producing them,” says Jim Dearing, solutions manager of physical access control, HID Global, Austin, Texas. “The latest inkjet printers for industrial card personalization deliver better quality at lower cost than ribbon-based technology, along with easier deployment, upgrades, and maintenance than possible with large central issuance machines. There are also new ways to issue and personalize ID cards. Cloud-based issuance platforms enable remote management of all card design, encoding to printing.”
Others believe in full obsolescence.
“I don’t know the exact timeline when [keycards] will become obsolete, but we are seeing a lot of requests from multiple customers, especially enterprise customers who are are shifting toward mobile credentials,” says Karmakar of Honeywell.
Brach Bengtzen, director of marketing at ProdataKey, Draper, Utah, adds, “I think that one of the big reasons why physical credentials are still out there is because people are used to what has always been working.”
Cyber Hardening Readers & Credentials
Despite their ease of use, readers and credentials face the same cyber problems as other devices in the industry.
“Any reader tied to the internet, including Wi-Fi, is vulnerable to the same issues of other IoT devices and must follow current network security protocols,” Ito of Camden Door Control says. “Closed network readers using BLE or UWB are more isolated from being hacked.”
Having unencrypted mobile credentials is just as risky as having easy-to-replicate prox cards.
“Unencrypted credentials can be easily cloned and copied, so using encrypted credentials, like mobile credentials or MIFARE DESFire cards, can help bolster your security,” James Segil, vice president of access control at Motorola Solutions, Chicago. “Your system is only as secure as the weakest link.”
The adoption of the Open Supervised Device Protocol (OSDP) has allowed readers to be more cybersecure (see “OSDP Versus Wiegand” sidebar). Dearing says upgrading to essential security features like secure messaging, mutual authentication and a random unique identifier (UID) can also better protect user privacy.
“These features can also help mitigate the chances of more complicated attacks such as man-in-the-middle attacks,” he adds.
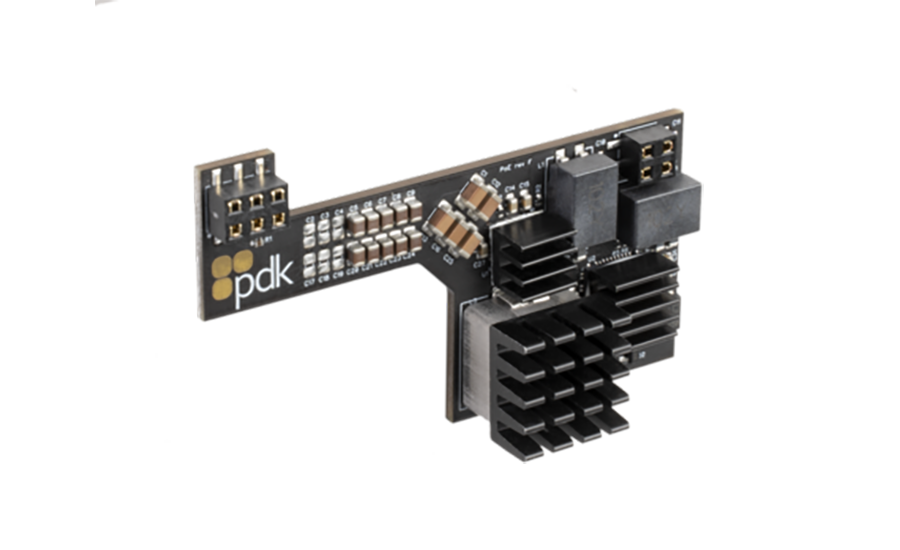
ProdataKey (PDK)’s PoE++ Module Kit is an expansion module that equips any pdk Red high-security door controller with PoE. When plugged into the controller’s board, the PoE++ Module powers the board itself and all the electrified hardware connected to it. The result is simplified installation and reduced cable runs that deliver savings on both labor and materials. // IMAGE COURTESY OF PRODATAKEY
Bluetooth & Beyond
Many believe that mobile credentials and readers will be integrated with other capabilities, like time and attendance, wellness checks, emergency response, smoke or CO2 detection, video integration, built-in microphone and tailgating detection, just to name a few.
“The simple piece of plastic on the wall will become the first-impression experience in any smart space,” Sczygiel of Brivo predicts.
Additionally, expect improvements to the technology, including less latency when using, leveraging more powerful processors in new smartphones. The positive experience for occupants, and the security for administrators, will justify the higher installation costs. “Readers and credentials will play a key role in driving many significant trends, from digitization to cloud-based identity management to mobile credentials that are part of increasingly integrated systems,” Dearing says. “Readers and credentials will also continue to be integral elements of enabling contactless building access and more frictionless access experiences, helping people safely return to work, school and other activities.”
And, expect a stronger bond between physical security and cybersecurity, even more multi-factor authentication in readers, including biometric authentication, and an emphasis on readers that connect to touchless solutions.
“As we see mobile grow, will there even be a reader on the wall next to each door anymore? We will have that answer before long.” Fergerstrom says.