Access Control
Security Readers & Credentials Evolve
Options in the world of access control readers and credentials continue to grow — but which is best for your project?

The issue of returning to work after the pandemic has accelerated the improvement of credentials and readers.
IMAGE COURTESY OF FARPOINTE DATA

Readers and credentials have become a part of our everyday life, though some might not realize it.
IMAGE COURTESY OF ALLEGION

As end users rely on their mobile phones for more and more, it’s only natural that they want to access buildings from those same devices.
IMAGE COURTESY OF SAFETRUST
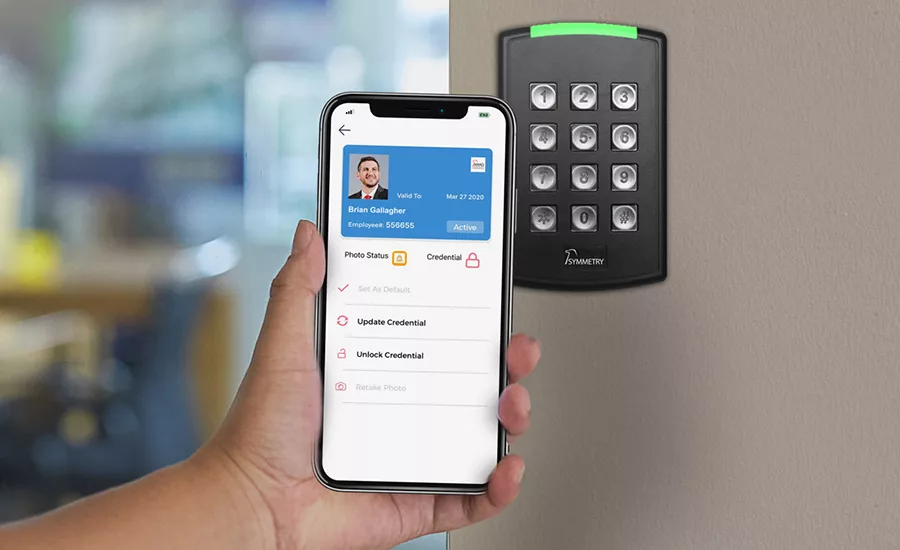
The adoption of mobile credentials continues to grow quickly for a number of reasons.
IMAGE COURTESY OF AMAG TECHNOLOGY
ACCESS CONTROL READERS AND CREDENTIALS have certainly come a long way in the past decade. The technology has now almost completely replaced traditional locks and keys, and the variety of products available is vast.
“Readers and credentials have become a part of our everyday life, though some might not even realize it,” says Brian Marris, product manager of readers, controllers and credentials at Allegion, Carmel, Ind. “When you check into a hotel, you expect to receive a plastic card or to be able to load a mobile credential to your phone. If you were handed a brass key for your hotel room, you would be surprised. … Most large corporations leverage physical credentials. Universities are moving … to physical or mobile credentials. Healthcare facilities have been using physical credentials for access and identification for years.”
Opportunities abound for security integrators and dealers in the credentials and readers space. As Marris points out, the market is getting smarter, and with that, it’s realizing the access control technology that’s been around for years is outdated.
“Historically, a credential was simply a card that came with an access control system — not much thought was put into the credential itself,” says Lisa Corte, director of product management, access and egress hardware group, ASSA ABLOY Opening Solutions America, New Haven, Conn. “Today, with the increased capabilities of access control systems and credentials, there is greater flexibility to choose the credential that works best for the needs of each facility. There is also much greater flexibility in the form factor of the credential. From the traditional card to the mobile phones and wearables, a credential can exist in many forms.”
Readers and credentials have evolved even more in the past year, as manufacturers worked to provide solutions for the “new normal.”
James Segil, co-founder and president of Openpath Security, Los Angeles, says that his team has tweaked many of their capabilities to be more relevant in a post-COVID-19 environment. “We’ve put a lot of capabilities in place to help with social distancing and to help enforce some of the rules put into place,” he says.
While analytics are one way in which access points can be better utilized during the pandemic, an increased awareness around germs has brought about a push for touch-free credentials and readers.
Looking for quick answers on security topics? Try Ask SDM, our new smart AI search tool. Ask SDM →
“COVID-19 has had a major impact on the reader and credential market,” Marris says. “Today, the market is evaluating ways access control systems can not only provide a more seamless experience, but a touchless one — all while maintaining increased security, of course. Everyone wants people to be able to move securely through doors with [fewer] touchpoints.”
And as all of these changes happen in the market, end users are becoming more informed about their options, meaning the security systems integrator needs to be more informed than ever.
“End users have become much more educated on how reader and card technologies work,” says John Becker, vice president of global sales, AMAG Technology, Hawthorne, Calif. “Ten years ago, the perception was that proximity was secure, and now the perception is that it’s not secure — people are realizing there are unsecure technologies. There are also expectations from customers that readers will support technologies like high-frequency cards and mobile, and potentially biometric as well.
“Customer expectations have increased. If a customer wants a combination of cards and mobile, for example, they know they can have this now and won’t settle for just what an integrator or manufacturer suggests.”
Wiegand & OSDP
Cyber vulnerabilities likely aren’t the first thing that comes to mind when most think of access control. But as devices become increasingly connected, integrators need to be sure that cybersecurity is top of mind.
“Cybersecurity is becoming more of a concern and consideration when dealing with a variety of readers and credentials,” says Brian Marris, Allegion. “The risks aren’t new, but as more systems become connected, it’s important for end users to take a closer look at the security protocols in place.”
The convergence of IT and physical security has also put an increased spotlight on the cybersecurity of readers and credentials.
“Readers and credentials that were once considered secure have been exposed through pen testing and other means, and proven insecure,” says Rob Brooks, Safetrust. “Yet, many customers are only now taking steps to secure their facilities with reader and credential technology that meets current InfoSec requirements and updated security tech. As security systems merge with IT, we are now seeing an increased desire to make sure access control technology meets updated IT security requirements.”
For years, Wiegand has been the industry standard to follow when securing access control systems. But, according to Farpointe’s Scott Lindley, it is no longer inherently secure due to its original obscure and non-standard nature.
“Plus, the multiple definitions associated with the Wiegand name have created confusion over the years,” Lindley says. “OSDP moves us forward.”
OSDP, or the Open Supervised Device Protocol, was developed by the Security Industry Association (SIA) and was approved as an international standard by the International Electrotechnical Commission in May 2020. Version 2.2 was released in December 2020.
The standard helps security equipment such as credentials and readers from one company interface easily with control panels and equipment from another manufacturer.
“In other words, OSDP fosters interoperability among security devices,” Lindley says. “It also adds sophistication and security benefits through features such as bi-directional communication, encryption and read/write capabilities.”
ASSA ABLOY’s Lisa Corte, says the comparison of OSDP to Wiegand is very similar to that of smart cards and prox: “Wiegand is fast and convenient but also less secure. OSDP is gaining traction because it provides a higher level of security in processing information from the credentials back to the system,” she says.
“Over the years, credentials have been getting smarter and more secure — but only recently, with OSDP, has the connection between the reader and controller caught up,” says Jacob LeRoy, customer support specialist, Cypress Integration Solutions, Lapeer, Mich. “OSDP being a two-way protocol instead of just a one-way data connection brings access control into the 21st century. Wiegand connections became popular in the 1980s, back when bag phones were the latest technology; cell phones have evolved dramatically since then, but Wiegand has not.”
Integrators’ options for migrating end users to OSDP are somewhat limited at the moment, but LeRoy says we should see more OSDP verified devices soon. In the meantime, Cypress offers Wiegand-OSDP converters to help integrators gain the advantages of OSDP while keeping some of the existing Wiegand hardware.
“OSDP offers much better security over Wiegand, and also allows readers to be modified and monitored by the head end software for greater user control,” says dormakaba’s Scott McNulty. “However, the lack of knowledge about the benefits of OSDP in the market, as well as the overwhelming majority of existing access control wiring, will keep Wiegand available for some time.”
Still, the importance of switching from Wiegand to OSDP in a timely manner cannot be overstressed. “Organizations that don’t move to OSDP-based access control solutions leave themselves extremely vulnerable to security threats, and miss out on its valuable benefits,” says Stephen Carney, HID Global.
The Problem With Prox
The migration away from proximity cards has been happening for a while now, but the pandemic has pushed fast forward on the move.
“If the question is what people are going to use going forward, I just can’t imagine we’re going to continue to see a lot of prox, or at least a lot of prox by itself,” says Jeff Nigriny, CEO, CertiPath, Reston, Va. “There will be a big push to what we’ve been seeing in Asia, with this cultural germaphobia.”
Cybersecurity concerns have also increased throughout the pandemic, and it’s become clear even to end users that many proximity cards can be easily cloned.
“Current RFID devices, particularly those operating at 125 kHz, are not suitable for secure identification,” says Scott Lindley, general manager of Farpointe Data, San Jose, Calif. “Proximity credentials that operate at 125 kHz are vulnerable to cloning. Credential holders have easy access to devices that make copies of their cards at retail stores, or they can purchase an inexpensive card cloner online. This allows copies to be given to unauthorized individuals who then gain entry using that employee’s identity.”
The smart card has proven itself to be a superior physical credential to the prox card in most applications. It is cybersecure, long-range and can even be contactless.
Interoperability, however, remains a challenge with the smart card.
“There has been a clear shift from magstripe and proximity to smart, 13.56 MHz encrypted credentials,” Marris says. “The struggle to date has been the ability to provide a secure physical credential that is as interoperable as a proximity credential. Proximity credentials can be used on almost every reader and electronic lock in the market. Due to the secure nature of smart credentials, many times, smart credentials can only work if they are provided by the same manufacturer who provides the reader or electronic locks.”
Allegion is currently focused on addressing this problem by using end user entity-owned keys, and by forming a partnership with the LEAF Consortium, an association of partner entities intent on bringing interoperability to the access control and identity credentials market and beyond.
Though prox cards might phase out, there will certainly be a place for cybersecure smart credentials in the future, as some end users will likely be against certain advanced credential technologies due to privacy concerns.
“While mobile credentials and other alternatives to physical cards (facial recognition, video analytics, etc.) are becoming more and more popular, there are a number of reasons why I don’t think cards will completely disappear in the near future,” says Scott McNulty, senior product manager, dormakaba USA, Indianapolis. “Some users will have privacy concerns around facial recognition, some don’t want to have a credential on their mobile devices if not company provided, and then there is also the added benefit that traditional cards offer low cost and convenience. In addition, some people who may use mobile credentials like having a card as a backup.”
Other Credential Options
Though they may be what you hear about the most, physical cards and mobile credentials aren’t the only options.
Smart watches and wearables, for example, have been growing in popularity in the credential space.
“Wearables are an increasingly popular authentication option for access to buildings; doors and assets; manufacturing systems with compliance traceability requirements; healthcare and defense markets; and other hands-free applications where users may not be allowed to carry mobile devices, cards or fobs,” says HID’s Stephen Carney.
COVID-19 has significantly increased the adoption of these wearables, CertiPath’s Jeff Nigriny points out.
“Certainly people still want speed of transaction at the reader, and now with COVID-19, we’re going to see more modalities that are contactless or based on a wearable,” Nigriny says. “You’re going to see an explosion of smart watches being used.”
While biometrics like fingerprint readers were gaining popularity a year ago, that is one area of the market that has taken a hit during the pandemic, as the idea of visitor after visitor placing their fingers on the same reader has understandably become a concern.
There is still opportunity in other biometrics as credentials though. Facial recognition, for example, is a completely touch-free credential that could work well in the “new normal.”
Mobile Credentials
Not only are customers moving from proximity cards to smart cards, but many are requesting to move directly from proximity cards to mobile access credentials.
“The ability to use mobile phones as access credentials is one of the biggest trends in a market that historically has been slow in adopting new technology,” Lindley says.
According to HID Global’s 2021 State of Physical Access Control Report, more than half of companies have already upgraded to mobile credentials, are in the process of upgrading to mobile or have plans to deploy mobile access in the future. In 2019, only 31 percent of companies were at the same stages of deploying mobile solutions.
“Mobile continues to grow very quickly, for a number of reasons,” Corte says. “Not only are there growing expectations from credential holders to have the same level of convenience they have in other areas of their life, but mobile also provides an added layer of convenience for the person issuing credentials, much like cards improved the process of managing brass keys.”
Openpath offers a mobile badge that looks just like a physical credential, with the end user’s photo and other information displayed in the same way. Segil says that mobile credentials have become more convenient in the world of remote working, because administrators can change the credentials in real time, from anywhere.
“With the digital badge, you can change characteristics as the world changes,” Segil says. “You can indicate whether they’ve been vaccinated, or any other status for that matter. These are the cool things about having a real-time credential on your phone rather than thousands of badges distributed to your employees.”
Stephen Carney, vice president of product marketing for physical access control at HID Global, Austin, Texas, says that COVID-19 has increased the demand for mobile credentials that deliver a more convenient, efficient and secure authentication experience.
HID is continuing to focus its research and development on mobile credential technology as a whole to expand a platform and ecosystem that is independent of transport technology.
“Ultra-Wideband (UWB) is a newer emerging technology that HID expects will become ubiquitous on mobile devices in a few years,” Carney says. “UWB technology provides the ability to deliver unprecedented accuracy and security when measuring the distance or determining the relative position of a target.”
It is not HID’s expectation that UWB will replace NFC or Bluetooth. Rather, Carney says the team believes UWB will work as a supplement alongside Bluetooth to provide the assurance, reliability and granularity of device position to enable a truly seamless access experience.
Openpath uses a triple unlock technology that sends commands over Bluetooth, Wi-Fi and LTE. The first command to hit the access control system unlocks the door, and the others are dismissed.
“One thing we noticed in the last two and a half years is that people still don’t want an app — they like the ease of the badge,” Segil says. “So we rolled out a technology called touchless access that gives the customer the ability to walk up to a door, wave their hand in front of the reader, and the door will unlock.”
They developed the technology in just one weekend in order to help customers keep buildings as touch-free as possible.
David Ito, product manager, Camden Door Controls, Mississauga, Ontario, says that COVID-19 has generated a high demand for no-touch solutions for door access.
“Clients are asking about smartphone solutions and hands-free solutions without compromising on security,” Ito says. “The challenge is to prevent false request-to-enter requests by an individual walking near an access point, versus a valid entry request. New technologies are emerging to resolve this issue.”
As mobile credentials are being adopted more and more, Lindley warns against using old solutions that have been retrofitted for mobile use.
“It’s easy to detail how and why mobile access is safer, but before we do, we need to understand that, like many recently introduced innovations, the problem isn’t with the new technology — it’s how the industry tries to retrofit the old system into the new,” Lindley says. “One potential hindrance is that some access control companies are trying to kluge their present offerings into new mobile solutions.
“Bottom line is that the mobile credential solution needs to have been designed to be a mobile-first solution — not just a hastily produced option to the old card reader solution. Yes, it should work in conjunction with the card-based system, but it should not be an offset of it.”
Readers
Readers have not been exempt from the changes the market has been going through in recent years.
“Readers were previously viewed as functional devices focused on user convenience,” says Rob Brooks, senior sales engineer, Safetrust, Fremont, Calif. “These days, organizations seek readers that can do more than a traditional building access device, like the ability to monitor building conditions, movement of objects and grant access to employees. As building access merges with IoT, readers will communicate with each other, passing critical information within a MESH network.”
As buildings start to switch from prox cards to other credentials, it’s helpful to use adaptable readers.
“Readers that are flexible to accept a lot of different credential types — a swiss army knife approach — would be a good thing,” Nigriny says. “I feel like I have a slightly different credential type for every customer we’ve got, and the readers that do better deal with that. The other thing that’s interesting is that some readers are particularly adept at aiding in transitions. If you’ve got a customer with prox now, there are a lot of readers that specialize in dual modes, which is a great selling point — otherwise your employees are walking around with two badges.”
AMAG’s Symmetry Blue reader is a good example of this. The readers deliver a transition path to end users who currently use proximity technology and want to upgrade to a secure, intelligent smart card credential platform with Bluetooth.
“Users can upgrade from proximity to smart cards to mobile with Symmetry Blue,” Becker says. “It provides a nice transition path to mobile, and users can migrate at their own pace or as budget allows.”
McNulty expects that the future of readers will be in embedded devices.
“We are already seeing signs of this with wireless locks, to the point where you can barely even tell that there is a reader incorporated,” McNulty says. “As mobile credentials and other touchless solutions continue to grow in popularity, there is no longer a need for a physical reader in the wall — simply walk up to the door with your phone in your pocket, and it unlocks.”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!