All in With Managed Access

Having trained and competent staff is critical to making the “service” portion of managed access control work.
PHOTO COURTESY OF INTO-ELECTRONICS INC.
There are many methods for making managed access control work, but all take away the hassle of the computer and server from the client’s site.
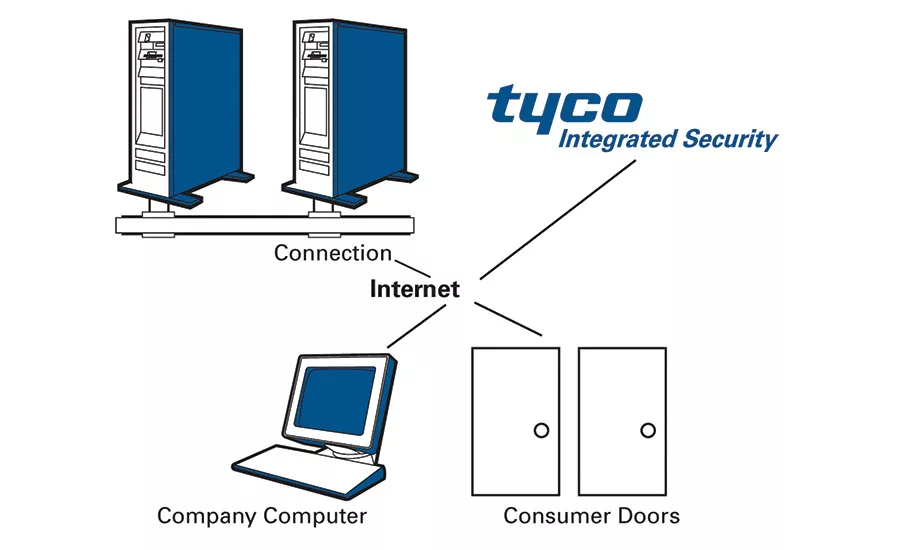
IMAGE COURTESY OF TYCO INTEGRATED SECURITY

IP connectivity and the cloud have provided the mechanism to offer the customer more at a reduced price with the ability to do it [remotely] through the cloud.
PHOTO COURTESY OF THE PROTECTION BUREAU

Managed customers are more demanding and you need to find the best way to communicate with them, whether through email, phone or text.
PHOTO COURTESY OF KEY-RITE

Many larger customers want to do more with managed services, leading to services that go far beyond just access control.
PHOTO COURTESY OF DUNBAR SECURITY SOLUTIONS
Integrators who offer managed access control often tell a similar story about how they got into it. Typically one or two key customers came to them and asked them to take over the managing of cards, updates and other tasks they found onerous.
Rod Wechsler, president, INTO-ELECTRONICS Inc., Toronto, says his company first got into managed access in 1993. “A client called me into one of their commercial buildings and spoke of the difficulty they had to go through in adding and deleting card holders on the fly. Then a big utility client had a lot of difficulties with software upgrades and updates. They asked us to take the software. Those are the main things that put us here.”
Bob Stockwell, chief technology officer, Stanley Security Solutions, Indianapolis, tells a similar tale. “What happened with us was a customer one day said he didn’t have anyone on staff to manage an access control system. He said, ‘I don’t mind buying and paying for it, but I don’t want an internal person to manage it. Would you be willing to put it in your office and make all those changes?’ We had never considered that, but we went back and forth and finally agreed. So the customer bought it and it resided in my office. We were getting employee photos in the mail to make cards and send them back to the customer. That is how it started.”
Times have definitely changed since then. With the proliferation of IP-based, Web-enabled systems and the cloud, there are more ways to offer managed access than ever before. SDMspoke with a number of highly experienced integrators in the managed access arena, who all agree that there are certainly promising trends, directions and opportunities if you do it right. There are good reasons to consider it if you haven’t already: There is a growing customer base for managed access control; it is easier than ever to do; and it brings coveted recurring monthly revenue.
“If you are an integrator and you haven’t thought about this, you really need to,” says Douglas Bear, director of operations for security systems, Dunbar Security Solutions, Hunt Valley, Md. “This is similar to 30 years ago where if you were an alarm installer you would set up a receiver and monitor it yourself, then figured out a big monitoring company could do that for you. From an integrator standpoint this is that same type of opportunity.”
Trends & Opportunities
Whether they were pulled into it by customer demand or made the conscious choice to offer this service, experienced managed access control providers say it has grown in popularity, particularly in the past few years — along with its cousin, hosted access, which still takes the server off-premise, but allows the end user to manage the day-to-day tasks themselves without having to worry about maintaining computers and software. Most integrators offer both options, or a hybrid. Both models are gaining steam, but managed access is more labor- and knowledge-intensive for the integrator — with potentially more ROI for the customer and RMR for the integrator.
Many customers today are more IT-savvy and understand the benefit to outsourcing, Bear says. “They understand more of the cost of managing networks and servers and databases and the personnel involved in that. As they are becoming more in tune with business needs, anything they can have managed by an expert seems to be the direction they want to go.”
Looking for quick answers on security topics? Try Ask SDM, our new smart AI search tool. Ask SDM →
SDM’s 2015 Systems Integrator of the Year Kastle Systems, Falls Church, Va., was founded in 1972 with a managed-only approach. Brian Eckert, executive vice president, says he often gets asked by colleagues how they were able to succeed in creating a managed platform. Today’s entrants into this market definitely have it easier, particularly with the advent of Internet and the cloud, he says. “Customers from virtually every industry are asking for it now because it is easier for them to do and it lowers their cost of ownership,” he says. “Now they can receive updates through the cloud and it offers a plethora of fantastic benefits. As that hook took place in the industry, everyone started to realize how much more convenient and flexible this was.”
The Protection Bureau, Exton, Pa. has watched the managed access industry change radically since the 1990s when it started offering the service using dial-up modems. “IP connectivity and the cloud have provided the mechanism to offer the customer more at a reduced price with the ability to do it [remotely] through the cloud,” says Marc Petrucelli, sales manager.
Some feel, however, the remote trend is hurting managed access control. “I think what technology has done is pulled people back from managed to hosted,” says Chris Diguardi, president, Key-Rite, Denver, Colo. “Now they can operate their system from a smartphone on the road.”
Kenneth Robison, co-owner, California Commercial Security, San Diego, agrees. “It has made it easier for the end user to do more of the management themselves. At the end of the day, when a managed client is sending in changes to us, there is still some tracking on their part to do that, so they might as well be doing it themselves online anyway because the tracking is right there. We are moving more towards hosted level of service.”
But others see the opposite effect. “We did it long ahead of the mobile phone era,” Wechsler says. “We hadn’t even thought about looking at things remotely. We have had some clients that wanted to move to a more interactive approach but not take back control completely. For the few clients that wanted to take it over, an equal amount decide to give it back. They decide they don’t really want that. Most clients are not looking for complicated. They only really want to see history.”
Rather than view it as a threat, those who focus on the managed side see this trend widening both the scale and scope of customers.
“We are seeing even smaller businesses embrace managed access,” says David Hood, director of business development, EPS Security, Grand Rapids, Mich. “That is where I have seen it change greatly. Our average per door, per account customer has come down. Years ago it might have been seven to eight doors. Today it is three to four doors.”
Hank Monaco, vice president of marketing, Tyco Integrated Security, Boca Raton, Fla., sees this as a great thing for smaller to mid-range customers. “Often trends end up benefitting mostly the very large customers. I really like to have things that take advantage of technology advancements and can be made available to mid-level and smaller businesses, which are often under strict cost constraints and lack the expertise to do a lot of the elements of access control that are required with traditional stand alone, or even hosted environments.”
While that mid-range smaller customer is definitely still the “sweet spot” for managed access, it is branching out in both directions. In some cases, the larger clients are starting to see the benefits. One reason for this, Robison says, is a change in attitudes. “I think that the IT side, which is where we saw pushback early on with managed access, they have become very comfortable with outsourcing email servers and all sorts of things,” he says.
“We absolutely see managed access appealing to larger customers in the future,” Bear adds. “We are seeing more and larger customers interested in having all of that pushed off as a managed service. It all comes back to IT. They are more willing to outsource that now. It is still in its infancy, but it is starting to gain traction and there are a lot more conversations about it.”
Dan Moore, branch manager, DAC Inc., Houston, says his company has been managing the access for a single client for the past seven years. But that single client has an enterprise-level system with 800 doors and 1,200 credentials. “We definitely plan to offer it to more [enterprise] clients,” he says. “When they are smaller it doesn’t matter as much; as they get larger it becomes a full-time position for someone.”
George Ballman, president of the Mid-Atlantic region and national operations for Kastle Systems, agrees with that viewpoint. “In my role in national sales I have seen much more traction with larger multi-office tenants that are national and even global. This has been a banner year for us with clients and we see a lot of companies looking for not just access control, but really a platform they can integrate into an HR system.”
Many of these customers are wanting to do more with managed services, leading to services that go far beyond just access control. Integrating access and video is another popular option. “We have the ability to manage both access and video,” Bear says. “We don’t host video, but we do integrate it in there. Much of our managed ‘access’ is integrated today.”
Monaco says on the higher end, “managed integration” is becoming more of a draw. “If we can integrate managed access along with other security applications where they can have it across the enterprise, that is a model we really aspire to, because we are then a fully fledged partner with our customers.”
Making It Work For You & The Customer
Ultimately that partnership is what truly sets managed access (or managed services of any kind) apart and where it is crucial to get it right. It starts with education — of the customer and your own employees.
“It is a process of education,” Bear says. “You have to explain to the customer that they can buy the software and the server and the backup server, provide the network and this is how much it will cost to stand that up. Or they can get it from us for X dollars a month. On top of that, there is the human capital. Are they going to just let us know what changes they need and we take care of it, or do they want to hire somebody or just give it to the receptionist? When you explain it that way they start to understand the value of it.”
This human capital is something the integrator needs to be prepared for, as well, Eckert says. “As a managed service there is a fair element of people and process that take over where technology may not be able to automate. You have to staff sufficiently and with care and knowledge to make a difference. A lot of companies that have dealt only in technology and not in managed services may miss the fact that the people are critical and central to the delivery of a great experience every day.”
Unlike client-based systems, the installation is only the beginning of the relationship — the most important part comes after that.
“They still have to be adept at the solution they manage and great at installing it,” Eckert adds. “But where the work and complexity comes in is after all that activity takes place. You have to deliver something every day that is reliable. It is less about the cloud or the method at that point and more about running a really sound practice with well-established procedures and knowledgeable people who can execute that.”
Wechsler agrees. “Programming a card for somebody to get in a building is relatively easy. But when someone calls you on a Saturday afternoon and says, ‘I need this card to be programmed for these four floors between 7 a.m. and 6 p.m. weekdays, 4 p.m. to 11 p.m. on Saturdays, and 3 p.m. to 9 p.m. on Sundays, you’d better have a very trained group to understand that and program it.”
Communication is key, in both the literal and figurative sense. “Figure out how they want those communications to flow,” Diguardi says. “It is important to realize managed customers are more demanding and you need to find the best way to communicate with them, whether through email, phone or text.”
On a macro level, make sure your salespeople are prepared to communicate the ins and outs of a managed access system. “The biggest challenge is getting the message to the customer correctly so they really understand what they are — and what they aren’t — getting,” Stockwell says. “This involves education, training and more training. There are a lot of folks out there selling that may not have been selling security that long. It’s important to get them comfortable and make sure the message to the client is correct and that they understand the benefits and tradeoffs…. Make sure they understand the difference between owning the head end and not, both on the rep and the customer side.”
On the sales side, there are many different approaches. Those who do the majority of their work in managed access typically lead with that approach and only do hosted or installed if the customer insists.
“There is opportunity, but you have to be all in it,” Hood says. “You need to have a culture where the entire organization leads with managed access, if that is truly what you want as a company. We really don’t provide the option unless the customer is extremely interested or really wants that control themselves.”
Selling managed access requires a different mindset that can be tough to shift. “We have been doing this for so long, but at this point the biggest challenge for me is still to get some of my older sales guys focused on selling managed,” Petrucelli says. “The lesson I have learned is if you really want to push the managed solution, there needs to be a focused approach with a separate salesperson than the enterprise guy.”
The RMR sales approach requires a different way of thinking for seller and buyer alike, but Monaco sees an upside. “It strikes me that all the trends are in our favor to promote that way of thinking. As more people involved in IT get involved in security, they are used to these services. And as technology becomes more available and the benefits greater we will have a fuller suite of offerings to give to our salespeople to sell.”
Robison advises, “Don’t be afraid to offer it. People will pay for it. This is definitely a shift and there are still a lot of integrators not selling it at this point. If they want to get into it, I think they should. It is the trend and it will become the standard if it isn’t already there…. Go for it as an assumptive close. That would be my recommendation. Also, really choose carefully and look at the products before you buy into one because once you start to install you are locked in. It is important to make a good choice up front.”
With integrators who have been offering managed access since the days of the modem — or before — the approaches can vary widely. However, there are some key considerations to keep in mind with looking for a manufacturer provider.
There are definitely all different types of architecture being used for managed access today, adds Brian Eckert of Kastle Systems. “There are so many types of companies in the security space from manufacturers to integrators. There are companies that haven’t architected their [legacy] solution to work in the way it needs to — not that they can’t go there, but there is a lot of work that needs to happen. Some software products don’t allow for remote access even today. There is a vast field of providers and the important part is being able to manage it — thus, the value of the cloud.
“From the integrator’s perspective all the demands a customer could have of you, the things that need to be done, the reports to look at and all those capabilities have to be exposed in that software and usable and auditable and trackable in order for it to be a relevant platform.”
While some specialize in one system, most have at least two or three options, some designed by them and others designed to work in the cloud.
“We have one primary and another option,” says Douglas Bear of Dunbar Security Solutions. “We use Tyco and DMP.”
Marc Petrucelli of The Protection Bureau says it is better to focus on a smaller number. “We try to be experts in a small bag of products versus offering a whole litany of products to everyone, and we have an even more focused approach on the managed side than the enterprise side, with a smaller product mix. ECKey is definitely one managed or hosted solution we like.”
Keith Lockhart, project manager, Operational Security Systems Inc., Atlanta, offers a mix of traditional and cloud-based solutions, which all require different methods. “For some, there has to be a server on-site and I will remote desktop into that server. With Feenics, it is cloud-based so there is not actually a server at the client site.”
Bob Stockwell, Stanley Security Solutions says his company consolidated from five to three. “I won’t allow us to get to one. I like to have at least two if not three because I need to know that I have choices and that customers have choices so it is not one box and one price. Brivo was born, bred and sold as a managed offering. Tyco and UTC we made that way.”
Rod Wechsler, INTO-ELECTRONICS Inc., says proper planning is key. “I would recommend they use access control manufacturers that are absolutely rock solid and reliable. There are a lot of manufacturers and they are not all the same. You have some that require firmware updates that you have to continually get.” Wechsler chose Mircom, DSC, Doorking and Avigilon and wrote Web interfaces to talk to them.
EPS Security utilizes five platforms, three of which are their main offerings (Honeywell, DSX and PCSC) due to application and their customer base, says David Hood. “Network connectivity is extremely important. We need to be able to connect to the customer’s space quickly, effectively and be able to make on-the-fly changes quickly and easily. We are connecting through network controllers directly at the customer site.”
Kenneth Robison says his company “grew up” with the Kantech solution they now use as one of their two offerings. “We have been using Kantech since 1995. We were pivotal in the creation of the managed solution they now have,” he says. “We are so deeply invested in that it is our core product and we have stuck with that. When we started using the software it wasn’t intended for managed access.”
While he is very happy with the solution they collaborated on, he says integrators today should use caution when choosing solutions that are not designed to be managed and trying to make them fit. “The products intended for managed access have sandboxed databases and are designed for multi-site managed solutions. While you can fake it using off-the-shelf solutions, it can be dangerous.”
With so much of managed access being done through the cloud or networks, a potential danger involves keeping your company and your customer’s site cybersecure.
“Cyber is the most concerning thing I have at the moment,” says Stanley’s Bob Stockwell. “When we sell a managed access control solution if the customer is going to put it behind their firewall I feel secure. But increasingly customers want to put two doors at the end of a DSL connection and the next thing you know there is no firewall at that location. For that scenario we offer a standard configuration of a firewall to encrypt the data.”
Douglas Bear, Dunbar Security Solutions, says he is getting more questions about that in recent years. If they don’t bring it up, he does. “Some customers come in asking these questions right off the bat. It is trending upwards because it is in the news. Every time you open the paper there is something about network security. When we say, ‘We are going to put this on your network,’ that should be their second question, after ROI.”
EPS Security’s David Hood agrees. “Network security continues to be a focal point that through our network, the customer’s network, and the manufacturer’s solution there needs to be encryption and firewalls in place that protect the end user. It is a conversation that is becoming a daily one. I believe in our industry we have to learn and get familiar with cybersecurity.”
Setting up your own side of things to be cyber-secure is just as key, says Chris Diguardi, Key-Rite. “Our criteria in selecting that was making sure the inbound port on a customer’s network did not have to be opened. We didn’t want to sell a system that would allow the customer’s network to be vulnerable.”
Kenneth Robison of California Commercial Security says cybersecurity is definitely a hot topic. “Fortunately our system is in a data center and all protected. Our firewalls are locked down for security purposes and we feel good about the steps we have taken.”
Dan Moore of DAC recommends making yourself an island. “We like to be behind a firewall and on a VLAN that separates us from their network. We want to be on an island by ourselves.”
MORE ONLINE
For more on managed access control, visit SDM’s website where you’ll find the following articles:
“Find Your RMR in the Access Cloud”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!