FIELD GUIDE TO NETWORKING: Expert Tips On Networked Systems
How can a client’s network be tested for its capabilities to connect security devices, such as DVRs and video servers?
Although typical Ethernet and Internet communications utilize common forms of addressing and infrastructure, each individual client’s network arrangement can and will be unique. Testing the configuration and capabilities of a particular network is very important when planning the installation of network-enabled security devices.
Typical tests for security installations would include Internet bandwidth testing, enterprise packet details, network traffic analysis, security scanning, and overall network configuration. There is a lot of activity and communications going on “behind the scenes†in a network. A number of software tools are available that will illuminate the performance of a network, and provide information regarding the effects of adding video transmissions to existing network traffic. Having these programs preloaded onto a technician’s laptop computer can provide quick testing capabilities and valuable information for network security system installations.
Internet Bandwidth Testing
To test for Internet bandwidth, connect the laptop to the client’s network via Wi-Fi or Ethernet, and visit http://www.dslreports.com/stest using the web browser. Follow the instructions, and within a minute or two test results will appear. Here’s an example:
Remember that the bandwidth indicated may be distorted by others on the network using the Internet connection at the same time.
Enterprise Packet Details
A very useful way of figuring out what’s going on with a particular network is by using a network protocol analyzer such as Ethereal, a free program available at http://www.ethereal.com. After following the instructions for downloading – including the downloading of an additional program called WinPcap – the Ethereal program will be placed on your desktop, ready for use. After turning on the software, simple selections can be made that will set up a “capture†sequence, copying all of the details of all packet traffic transmitted on a particular Ethernet network or segment. Once the capture has started, packets are recorded, and can be reviewed for their content. This can be a powerful educational experience for networking novices, as all packets are presented on the screen, and the behind-the-scenes workings of Ethernet can be viewed and analyzed.
Network Traffic Analysis
Graphic representations of network traffic are often useful to quickly determine what the typical levels of traffic are on a particular network, and what happens when a high-bandwidth device such as a streaming video server is connected. Available at http://lastbit.com/ trafmeter/Default.asp, the free version of TrafMeter can be configured to provide simple line-graph information, showing the overall amounts of network traffic and various subclassifications of Ethernet packet types. In the example on the facing page, the yellow line represents overall network traffic, while the green line shows the bandwidth consumed by a typical UDP transmitting video server. On a larger scale, IT personnel will use programs like TrafMeter to provide constant monitoring of their network traffic, allowing them to analyze network traffic and issues both in real-time and by later review.Outside Hacking Potential Testing
A major concern for any Internet-connected computer or network is the potential for hacking by outsiders. A simple and effective test for basic anti-hacking capabilities of a network’s firewall configurations is available over the Internet. Visit http://www.grc.com, and advance through the web page to the Shield’s UP! testing selection. This program will attempt to penetrate the ports of the network being tested, and will present results indicating which, if any, ports are open to outside penetration.
Overall Network Configuration
SyPixx Networks Inc., a supplier of fiber and Ethernet security networking interfacing equipment, is providing an innovative software package that graphically displays and monitors the individually addressed devices on a particular network. This program, called ClearMap, uses the “ping†command to constantly check for devices on a network, displaying their location, product brand, network name, and/or IP addresses. Graphics files can be associated with individual devices, so that a picture of the device or the instruction manual can be quickly retrieved and displayed on the viewing screen. Alarms can be generated if a device is removed, or if a new device is added to the network. When run on a network server, ClearMap provides a constant supervision of network devices, adding a critical security element to networking. Device monitoring software such as ClearMap is critical to high-security networking systems, because the addition of a wireless or wired rogue computer can open many possibilities for hacking, information theft, and network disruption.
Network Video Connections – Spreading the Bandwidth
Networking video signals provides great potential benefits for security companies and their customers, as video signals can be connected to existing cabling, sent over local networks and/or the Internet, and viewed and recorded in multiple locations. Due to large bandwidth requirements, it can be difficult to convince a client’s IT personnel to allow video encoders to be installed on their networks, as IT may fear that the video signals will crowd out other enterprise network communications.One important concept is that the specified 100 Mbps communications capability of a typical Ethernet network describes the communications between individual addressed devices and a switch or hub, and isn’t a cumulative bandwidth for the entire network.
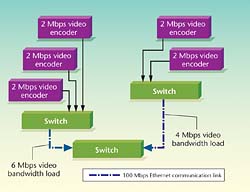
Which network switches are connected to video encoders will have an important impact on how much bandwidth is used for video on a particular network segment. Let’s look at an example (see illustration above).
Each switch connection provides up to 100 Mbps bandwidth, which is generally reduced to 50-60 Mbps because of cabling and equipment issues. If we connect five 2-Mbps video encoders to one switch, 10 Mbps of bandwidth between the switches will be consumed by the video streams.
Using longer coax connections between the camera and the video encoder can allow encoders to be housed and connected to the network in telecommunications closets far from a camera’s location. If an installation is planned so that the video encoder connections are spread among a number of switches, there is less impact on each network segment connecting the switches, and less effect on other enterprise data communications that are using the same segments (see graph):
Looking for quick answers on security topics? Try Ask SDM, our new smart AI search tool. Ask SDM →
Command Line Functions
There are many useful testing and confirmation tools available from the “command†line in Microsoft Windows. To reach the command line, click “Start,†then “Run.†In the dialog box, enter “cmd.†A box will appear on the computer screen, with a “C:>†prompt line. From here, technicians can test various network communications and receive local network addressing information.Here are some of the common commands, and their typical results:
- Ipconfig /all – provides complete addressing information about that particular computer, including MAC and LAN IP addresses and whether the computer received its address from a DHCP server.
- Ping – typing “ping†followed by a space and then a LAN or Internet address will send four packets of 32 bytes of data to the target device, which will send back receipts to the initial sending computer. Pinging a device verifies that it is connected to the network, and in the case of a LAN device, that the device is addressed to the same local network. If a device won’t ping, then it’s not connected to the same network or is addressed improperly.
- Tracert – Using “tracert†(trace route) will provide information regarding the path that data packets are taking from the subject computer to another location on the LAN or Internet. An example is to the right:
 Tracert shows all addressed routers located between the testing computer and the IP address being traced.
Tracert shows all addressed routers located between the testing computer and the IP address being traced.If there are difficulties getting communications across a network or the Internet, tracert can indicate at which router the communications are being stopped.
- Netstat –a – Provides a table of the current software port activity for that particular computer.
- Arp –a – Provides the Address Resolution Protocol (Arp) table for the computer being queried, showing the MAC and IP addresses of other devices on the network that have been in recent communication with the interrogated computer.
For finding the Internet IP address of a network, type www.whatismyip.com into the address line of an Internet-connected computer. The Internet IP address will appear on the screen.
Testing for Ethernet Capabilities
When connecting security devices to an existing network, security technicians can be confronted with problems not of their own making. Existing network cabling systems may or may not be in usable condition for the connection of network-enabled security devices.For example, let’s assume that a network-enabled intercom interface is to be connected to a specific open RJ-45 port in the telecommunications closet. It’s important to remember that the specific cabling and connector to be used within the telecommunications closet may have been incorrectly terminated, or may have suffered some damage from other technicians. There are three questions that need to be answered prior to the successful connection of the intercom device:
1. Is the RJ-45 female connector properly connected to the network?
2. Are Ethernet communications present?
3. What speed Ethernet (typically 10 or 100 Mbps) is available?
There are three possible ways to test for these important factors. If the intercom device in the example has already been addressed to go onto the network, the technician could plug it in, power it up, and see if it works. However this approach could cause the technician to assume that the intercom device is defective if it doesn’t work, when the problem could be in the cabling or Ethernet compatibility. This technique also would require that any management software be installed in the head-end computer, which may create cascading issues that can cause the technician to make incorrect assumptions.
Using a laptop, the technician could plug the computer into the target RJ-45 port, set the laptop for DHCP addressing, connect to the enterprise Ethernet network, and “ping†another computer on the network. If the ping is successful, the RJ-45 port is correctly wired, and the network is providing Ethernet communications. Clicking the Network connection icon on the Windows desktop will bring up a screen showing the connection speed, as illustrated here for a Wi-Fi connection:
This laptop test can work, provided that the network is set to issue DHCP IP addresses to any device connected to it, without any security or MAC level filtering. This type of testing is slow and cumbersome, relies on network DHCP addressing that may not be present, and can potentially damage the testing laptop if the RJ-45 port is miswired.
The third method is probably the surest test available. Inexpensive Ethernet testers, such as the Byte Brothers TVR 10/100, can be plugged into the target RJ-45 port, and within seconds indicate whether the port is correctly wired, Ethernet is present, and which data speed, 10 or 100 Mbps, is available. (Visit www.bytebrothers.com or call (425) 917-8380.) If the tester indicates a problem, the security technician can inform building management of the problem and ask them to fix it. Because of its speed, simple usage, and portability, this type of tester provides a great value to security technicians.
All RJ-45 ports to which network-enabled security devices are to be connected should be tested using one of these methods prior to starting an installation.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!


