The EYES Have It


As end users in government and industry become ever more security-conscious, they are beginning to realize the limitations of access control mechanisms that rely on identification cards. As Evan Smith, president of iris technology developer EyeControls, Herndon, Va., puts it, “People are recognizing that you’re identifying the card, not the person.”
Some end users opt for less costly fingerprint-based biometric solutions, which outsell iris readers by a substantial margin. But fingerprint technology has limitations, as well. “Iris recognition is more accurate than fingerprint recognition,” notes Smith. “There are more unique points of identification on an iris. If you take several fingers, you can get acceptable accuracy for access control.” But because most fingerprint readers used for access control use only one fingerprint, he says, “They’re more accurate than a card, but not necessarily a perfect identifier.”
For access control applications, end users generally are more concerned about false rejections (or rejecting the correct person) than with false acceptances (or accepting the wrong person). “People tend to tune the system so they avoid false rejections,” explains Smith. “You don’t want to keep the president of the company standing outside.”
In comparison, iris readers rarely accept the wrong person. The odds of two people having the same iris pattern are less than one in a million, according to Panasonic, Secaucus, N.J., which claims that its iris reader is 100 to 1,000 times more accurate than fingerprinting.
Another advantage of iris readers is that they do not require users to touch them, which can be critical in laboratory environments where people wear gloves, or where end-users are simply concerned about germs. Iris readers may be the only viable choice for certain types of users, says Steve Surfaro, group manager and industry liaison for Panasonic. For example, he says, contractors and other people who work with their hands often have cuts that can prevent them from using fingerprint technology. As a result, he’s seen significant demand for an iris-based Panasonic system that is designed to screen visitors, including regular contractors, entering building lobbies.
One systems integrator that installs iris technology is DRS Technologies, Parsippany, N.J. As Sandeep Kaul, vice president of business development and technology for DRS Technologies’ Technical Services unit says, “When it comes to accuracy, speed of recognition and the lack of physical contact, nothing is better than iris identification.”
How it Works
David Johnston, vice president of marketing for the Iris Technology Division of Cranbury, N.J.-based manufacturer LG Electronics, provides an excellent description of how iris technology works. As he explains, iris recognition involves taking a picture of the iris — the externally visible colored ring between the dark center, or pupil, of the eye and the sclera, or white, of the eye. “Once taken, the image is turned into a digital representation or template and stored in a database,” he says. “On subsequent occasions, additional pictures of the eye are taken, processed in similar fashion to template form, then compared.”These comparisons can take either one of two forms. With some systems, the user first presents an identification card on which his or her template is stored, and the system compares that image to the current one — a matching process known as “verification” or “one-to-one” comparison. With other systems, the current image is run against an existing database to find a match — a process known as “identification” or “one-to-many” comparison.
“One-to-many” is often the preferred matching method for iris readers because it does not require users to carry an identification card. That’s another advantage in comparison with fingerprint readers, which are more likely to use “one-to-one” matching. According to Smith, fingerprint systems tend to use “one-to-one” matching because a single fingerprint is not a unique identifier. That limitation complicates the process of finding a perfect match, particularly in a very large database. Although some systems integrators believe “one-to-many” matching can be too slow, he says that’s not a problem for iris-based systems. Such systems take about one second to accept or reject a person, and he says that’s acceptable to most users.

This portable, handheld iris recognition system is used by the U.S. Department of Defense to identify people on watch lists while in the field.
What’s it Going to Cost?
Iris-based systems actually can be less expensive than fingerprint technology when large user databases are involved, notes Bruce Hanson, president of SecuriMetrics, a unit of Stamford, Conn.-based iris technology developer L-1 Identity Solutions. Noting that iris records are significantly smaller than fingerprint records, he says, “Where you save money is in the amount of computing power and storage required on an iris system. The data is easily compressed, transported and stored; and in an environment where there are tens or hundreds of thousands of subjects, iris technology can be surprisingly inexpensive.”Typically iris readers are interchangeable with card or fingerprint readers and are connected to a full-blown access control system. But some new form factors also have become available. Panasonic, for example, offers a system that connects to a stand-alone personal computer. “It’s like a small management system for use without an access control system,” Surfaro says. “It’s what somebody with a single portal door and no access control system would want.”

DRS Technical Services has installed an iris reader from LG Electronics to accurately identify prison inmates.
Although the rise of handheld systems might seem to portend a reduced role for systems integrators, Hanson notes that integrators are as critical as ever because such systems need network connectivity in order to update, and receive updates from centralized databases.

Portable iris recognition systems are used in prisons to identify prisoners
Recent Advancements
In recent years, developers and systems integrators have demonstrated tremendous creativity in their application of iris recognition technology.DRS Technical Services, for example, has installed an iris system from LG in a number of jails to accurately identify returning inmates and inmates who are due for release.
Another highly beneficial application of iris technology is the Children’s Identification and Location Database (CHILD), a database of iris templates organized by the Nation’s Missing Children Organization to help recover missing children. Administered through sheriff’s offices in 25 states, the program uses Panasonic iris recognition equipment to voluntarily enroll children into the system.
Several advancements have been made in iris technology in recent years. For example, the cameras used to capture iris images are much easier to use than in the past, notes Cathy Tilton, vice president of standards and emergency technology for Daon, a Reston, Va.-based developer of software that underlies iris recognition systems. “It used to be that you had to be within a specific range. If you were too close or too far, the camera wouldn’t get you right. You had to open your eyes quite wide, and the camera was kind of picky about which way you were looking.” Today, all that has changed, she says. “With some systems, you just have to look in the general direction,” she says, adding that cameras are being developed that can even capture moving subjects. Such advances are reducing the response time of iris recognition systems.
Today’s systems also have technology in place to help ensure what Tilton calls, “liveness detection.” To prevent people from using a photograph of an eye or a dead eyeball to foil an iris camera, she says, some of today’s cameras look for involuntary behaviors, such as fluctuations in pupil size and micro-movements of the eye, to verify that a subject is a live human.

Iris readers can provide fast enrollment and authentication times. This BM-ET200 Panasonic reader provides authentication results in 0.3 seconds.
Smith adds that Iridian’s price structure was unfavorable for small installations. “You had to buy a license that started at 1,000 people and the base rate was five dollars per person enrolled. ” As a result, he says, “The whole industry has been stuck for 10 years in a volume-less operation.”
Smith expects to see prices come down substantially because, as volumes increase, camera costs will come down. “There is no reason the cameras have to cost $2,000,” he says. “They’re just ordinary cameras with a few tweaks to make them pick up a good image of an iris.”
Another key patent, which L-1 acquired through its purchase of Iridian, is due to expire in 2011. That patent, which was originally granted to iris technology expert John Daugman, covers an algorithm for matching iris images. Already companies such as EyeControls are developing alternative algorithms, and the National Institute for Standards and Technology has sponsored a competition for the best new algorithm, the results of which are expected to be announced in the near future.
Meanwhile, Hanson says, “Daugman is part of the L-1 group and he’s quite busy improving upon his already industry-leading algorithm.” For example, Hanson notes that traditionally some Asians have been unable to use iris recognition because the system could not distinguish their dark brown irises from their black pupils. But, as a result of L-1’s development work in what he calls “active contours,” the percentage of people who cannot use iris recognition has decreased by a factor of 10.
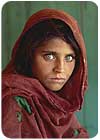
John Daugman, a pioneer in iris technology, confirmed the identity of an Afghani woman who appeared on a National Geographic Magazine cover 20 years earlier.
Sidebar: A Useful Resource
A wealth of information about iris technology can be found on a Web site operated by iris technology pioneer John Daugman at www.cl.cam.ac.uk/users/jgd1000/. Among useful material, you can read how Daugman used iris recognition to confirm the identity of the Afghani woman who 20 years earlier appeared in a famous National Geographic Magazine cover shot.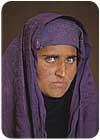

Travelers enroll at Registered Traveler pilot program kiosks at Los Angeles International Airport in the Summer 2004.
Sidebar: Registered Traveler Program Taps Iris Technology
Iris recognition technology is likely to gain greater awareness and acceptance as more and more airports begin to support the Transportation Security Administration’s Registered Traveler program. Now available in several U.S. airports, the program is designed to simplify the security screening process for people who travel frequently.Travelers pay $100 annually to participate in the program. The application process includes a security check and when an applicant is approved, he or she is issued a card that includes both a fingerprint and an iris template. “You enroll both and designate which is primary,” explains Larry Zmuda, a partner with Unisys, Blue Bell, Pa., which is one of only a handful of systems integrators approved to install systems to support the Registered Traveler program. “If you want iris to be your primary, when you insert your card, the system will ask to capture your iris.” The system, which includes both a fingerprint and iris reader, then will verify that the biometric matches the one stored on the card.
Registered travelers wait in a separate shorter line at the airport. “It provides predictability,” Zmuda says. “You now know how long it will take you. It’s less than a two- to five-minute wait versus an unknown wait, when you get to any airport.” Registered travelers still must go through a metal detector, but program administrators are considering some additional benefits, such as not requiring registered travelers to remove their shoes.
Unisys initially installed systems to support pilot tests of the Registered Traveler program in Los Angeles, Minneapolis and Houston, which were well received. “We found out that customers were willing to use biometric kiosks and did not find any apprehension to it,” notes Zmuda, adding that Unisys is currently rolling out a system at the Reno airport.
The equipment that Unisys selected to support the Registered Traveler program has gone through conformance testing to demonstrate that it is interoperable with other solutions. Zmuda notes that airports aren’t required to deploy interoperable systems, but he says it would be in their interest to do so. “The thought is to make sure it works like automatic teller machines,” Zmuda says. “Whichever bank you go to, your ATM card will work.”
Currently 40,000 people are in the Registered Traveler database. Zmuda says that number is expected to grow to between two and three million in the next year or two.

A4Vision offers a three-dimensional imaging facial recognition product used for access control applications.
Sidebar: Facial Recognition on the Rise
Although systems integrators may be most familiar with iris and fingerprint biometrics, another option that is likely to increase in popularity moving forward is facial recognition.Facial recognition technology used for access control typically is based on three-dimensional imaging, notes Grant Evans, CEO of A4Vision, a Sunnyvale, Calif.-based unit of Bioscrypt, which offers such a product. With the A4Vision system, Evans explains, three-dimensional images are captured using a fine mesh grid of horizontal and vertical lines that distort over the topography of a face.
Although two-dimensional images are used in other types of facial recognition technology, such as for passport photos, Evans says, “You won’t find two-dimensional facial recognition used in access control because of lighting, angle and movement.”
The big benefit of using facial recognition for access control is that it’s fast and convenient. As Evans explains, the A4 system typically uses a “one-to-many” approach and requires little or no cooperation from the people who are being screened. A “one-to-many” approach matches images against an existing database to find a match; therefore no identification card is required for entrance. “As soon as you come into the field of view of the camera, it has the ability to match you with some other data,” Evans says.
Typical organizations using facial recognition for access control include high-risk profile enterprises with 5,000 or more employees, notes Evans. “They tend to sit in banking and finance, pharmaceuticals and transportation, or are Fortune Global 500 companies,” he adds.
A Swiss bank, for example, is using A4Vision technology to support “speed gates” that enable 4,000 employees to come through three doors in 45 minutes. The technology also supports the bank’s time and attendance system and is used in combination with iris recognition and a PIN code to control access to safe deposit boxes.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!



